Students Lead Spring Semester Projects that Support Intelligence Analysts

Students play a vital role in research at the Laboratory for Analytic Sciences. From design to computer science and data prioritization, we’re spotlighting four of this year’s research projects at LAS led by NC State and Winston-Salem State University students that will make an impact on national security.
NC State Design Students Unveil New Concepts for Language Analyst Interfaces
Work completed this semester by seven students in the Masters in Graphic and Experience Design program at NC State has successfully made its way into the intelligence community. Through LAS collaborator and NC State College of Design professor Helen Armstrong’s design studio class, students developed prototypes of artificial intelligence-infused tools that would give voice language analysts a way to quickly produce reliable intelligence.
Since the end of the semester, the students’ concepts have been viewed by hundreds of analysts, managers, and software developers. In a survey seeking feedback from language analysts, LAS project leaders received nearly 70 responses.
“The final prototypes beautifully integrated AI throughout the workflow, pushing the envelope of what might be possible in the world of language analysis,” says Patti Kenney, a language analyst at LAS who gave students feedback on their ideas.
The challenges that come with understanding the nuances of spoken languages, like regional dialects, slang, and casual conversation, became clear to the students.
“I didn’t realize that you had to listen so much,” student Diksha Bahirwani says, referring to language analysts who scan voice recordings, often in foreign languages, for important details. “Nobody announces what they’re going to talk about before they talk about it.”
In the real world, designers also usually have an initial concept from which to base their ideas for refinement – upgrading an old website or improving a roadway intersection, for example. Because of privacy restrictions, however, Armstrong’s students were not able to view the software and tools currently in use by intelligence analysts.
“For designers, we always look at improving a design, and this was like starting from scratch, without any reference to what kind of features you guys use,” Bahirwani says. Students based their interface prototypes on conversations with LAS language analysts and incorporated feedback received from critique sessions.
“It was clear the students had come to deeply understand the language analyst workflow and that designing for these workflows from the vantage point of [College of Design building] Brooks Hall – from the outside in – contributed to the success of their work,” Kenney says.
Winston-Salem Computer Science Students Develop Synthetic Data for Cyber Analysts
This semester, LAS analysts also partnered with a class of 11 seniors at Winston-Salem State University (WSSU) through the Educational Partnership Agreement and/or Cooperative Research and/or Development Agreement. Their project focused on creating synthetic data knowledge graphs that could improve security within a cyberspace domain by training both cyber analysts and machine learning models. Synthetic data is artificially generated by a computer simulation and works as a stand-in for data from real-world events, which may contain sensitive or private information.
Applying knowledge graphs – visual displays of relationships between entities – to the cyber domain helps intelligence analysts better understand and visualize data.
“These graphs represent objects like cyber attacks, viruses, malware, descriptive information about adversaries, or networks, which can help analysts uncover relationships between objects,” says Al Jarmon, an LAS analyst who collaborated with the students at WSSU. “Our students made restriction-free knowledge graphs that will enable national security tool builders to build better algorithms. ”
The students used the computer programming language Python to generate high-quality synthetic knowledge graphs of cyber campaigns based on various input parameters that are exportable to STIX 2.1 (Structured Threat Information eXpression), a language and serialization format used by LAS analysts to exchange cyber threat intelligence.
“This partnership exposed students to real-world national security mission problem sets, which allowed them to develop interests in continuing collaboration and/or employment opportunities with NSA,” Jarmon says.
NC State Computer Science Students Enhance Data Prioritization and Visualization Prototypes
As a capstone research experience, the Senior Design Center of the Computer Science Department at NC State assigns real-world problems to groups of graduating seniors during their final semester. This spring, two teams of computer science students tackled LAS-related projects.
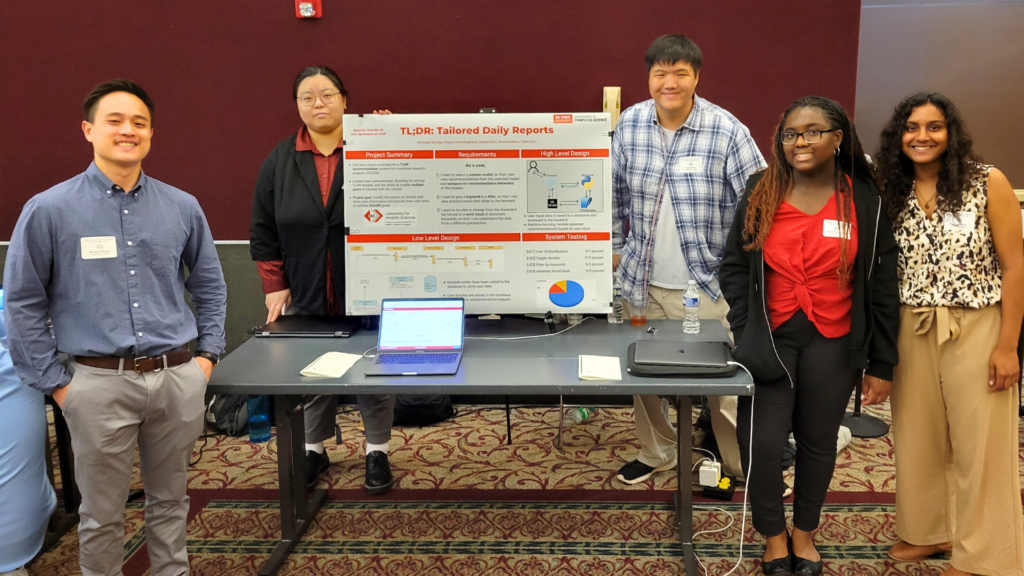
The first group of five students built on the work completed last summer by researchers on a tailored daily report (TLDR) software prototype for intelligence analysts.
“Since we wanted our next group of summer researchers to focus on the AI, summarization, recommendation, and human-computer interaction aspects of the TLDR, we posed the task of boosting user-experience functionality to these talented seniors,” says Sean Lynch, a researcher at LAS.
The students created a feature that allows users to select which recommendation engine they would like to use; bolstered the prototype’s ability to handle multiple users at once; and developed a way to offer users a word cloud of recommended news articles. In addition to the text summaries of the documents presented, this gives users a quick triage capability to determine which documents they may want to review in detail.
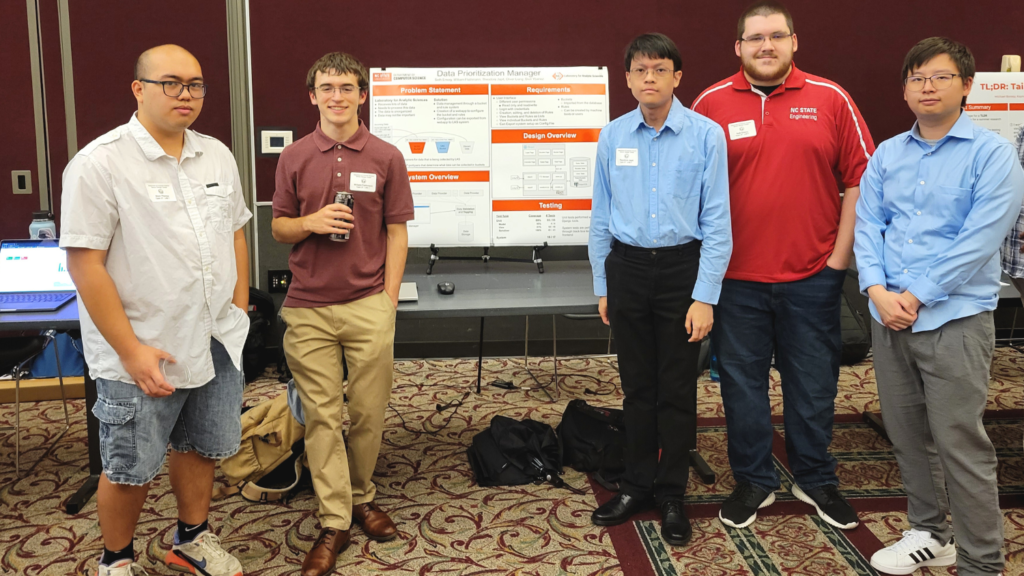
The second team of five students built a data prioritization management application from scratch.
“Cyber security analytics looking to detect fraudulent or nefarious activities may have to process very large amounts of data, and quickly,” Lynch says.
With growing data volumes and access to faster communication infrastructure, building machine learning models that scale to modern data throughput levels is a difficult challenge.
“The student team developed a new full-stack web application using [programming language] Django as a back-end framework with all the essential functionality we requested, like a React front end, and a database storing rules, buckets and user information,” says Lynch.
Both student teams also drafted a user’s guide, a developer’s guide, and an installation guide. This information will be essential for the next group of researchers who will build upon the students’ work and continue addressing these complex problems.
This post was originally published in Laboratory for Analytic Sciences.